Do I Need JWTs?
Twice I’ve been asked “do I need JWTs”. Twice I’ve given the same answer. Which means it’s time to document/automate my answer before I get asked a third time.
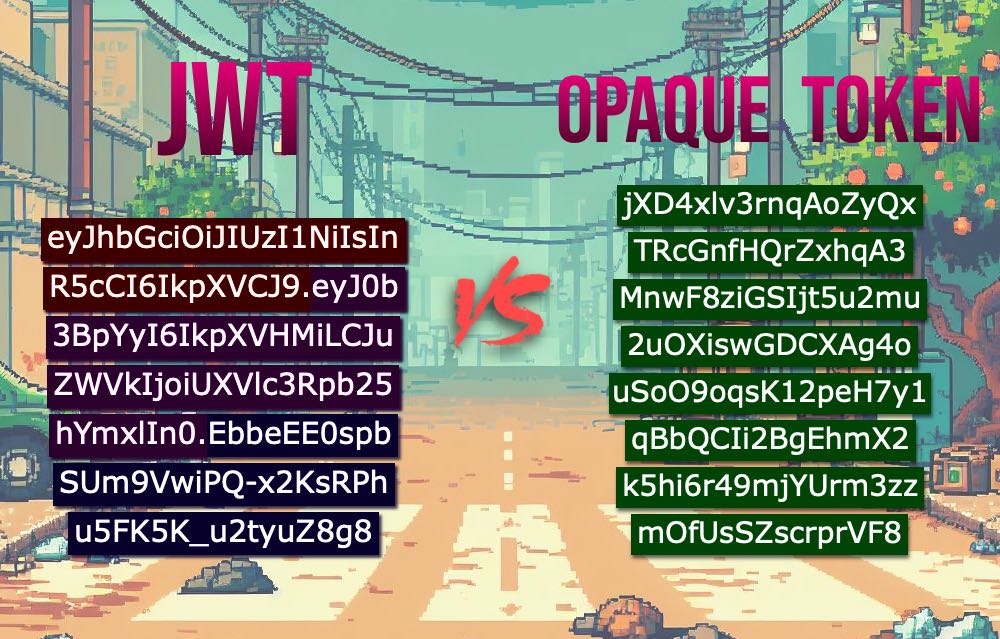
The first part of my answer is that a better question would be, “do I need stateless auth?” JWTs are technically just a message format that are designed to be used with stateless auth, and that’s what you really want to ask yourself.
The second part involves me drawing things.
Do you have a single RESTfull monolith service deployed on a single server?⌗

Stick with stateful auth via an opaque token. You’re already opening up a connection to the database with every RESTfull call, and adding in one more database query to return a single row from an indexed table is just not going to add a noticable bump to your time.*
Do you have multiple services colocated in one datacenter?⌗

Build a single auth service, that implements stateful auth via an opaque token. Put it behind a Redis cache to make it fast. Any service can call that auth service to get the user’s auth state. The time it takes to make calls withing a local network is on the order of 500μs, and (probably) isn’t going to make a bump on your time.†
Do you have multiple services in multiple datacenters?⌗

Now, maybe, you need JWTs, and all the decentralized stateless authorization that comes with it. There are still other options, depending on your architecture, but this is still the first time I think people should think about stateless auth.
Of course, if you’re using an Auth-as-a-Service, you are immediately at this stage.
Endnotes⌗
* I previously worked for PropelAuth, and I think their stateless auth is top tier, but I have to give it up for SuperToken’s blog for gathering some nice evidence on this point: https://supertokens.com/blog/are-you-using-jwts-for-user-sessions-in-the-correct-way
† 500μs is taken from the classic Latency Numbers Every Programmer Should Know, https://colin-scott.github.io/personal_website/research/interactive_latency.html .
Some of these drawings are obviously and poorly hand made, and here’s a behind the scenes look at it.